|
Legal authority
|
The legal mandates under which an item was collected, created, received or used.
|
|
Purpose
|
This attribute identifies the legal authority or authorities which are used to classify an item according to its governing legislation, streamlining action to ensure its compliance.
|
|
Commentary
|
The legal authority may include Memorandum of Understanding (MoU); Legislation; Machinery of Government (MoG); Government policies or acts. It may also include the authority, e.g. (Australian Government) Federal Register of Legislation or Data Availability and Transparency Act 2022.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided.
- Where a desired value is not listed contact metadata.management.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Purpose
|
The primary reason the data was collected, created or shared.
Program data, Operational performance data, Corporate workforce data
|
|
Purpose
|
This attribute defines what type of data was collected or created, supporting the identification of custodianship, publication responsibilities and contributions to the Australian Government Data Catalogue (AGDC).
|
|
Commentary
|
The terminology is sourced internally and consistent with key performance measures and reporting.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select a single value from the options provided:
- Program data: data captured specifically for the purpose of administration and payments for programs across social welfare, child support, health, veterans and aged care sectors.
- For example, customer/patient circumstances data.
- Operational performance data: data that enables or supports the delivery and assurance of the internal services that are required to operate programs.
- For example, phone statistics, service officer statistics, claim/processing statistics.
- Corporate workforce data: data about the agency itself and its employees.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Purpose details
|
The detailed reasons the data was collected, created or shared.
|
|
Purpose
|
This attribute provides additional business context by describing the purpose for collecting, creating, receiving or otherwise holding data, ensuring data is used as intended, and supports compliance with the Privacy Code.
- It answers the question: Why was the data collected or created?
|
|
Commentary
|
The purpose details field is used in conjunction with the Definition and Keywords for identifying and describing the purpose for which the information was collected and is required for all items that contain personal information. This is required under the Australian Government Agencies Privacy Code requirement for agencies to maintain records of personal information holdings.
|
|
Controlled values
|
- At least one complete sentence or a collection of dot points which explain how data is used.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
- This data asset is used to collect and maintain a record of new staff employed by the agency, providing SES oversight of workforce status, attrition and new hire volumes within a rolling 12-month period, it supports adherence to the ASL staffing cap by recording over or under spending on recruitment activities. The information further informs SES when undertaking recruitment activities and contributes to financial year reporting requirements, corporate reporting and registered ICT user account creation.
|
|
|
Executive data steward
|
The executive data steward accountable and responsible for the data and this record.
|
|
Purpose
|
This attribute facilitates the unambiguous identification of the executive data stewards and provides stewards with insight into the data for which they are accountable.
|
|
Commentary
|
The executive data steward is responsible for coordinating data governance at the branch level and managing data specifically relating to their position and authority, including the business outcomes their business units need to deliver. Their functions include promoting compliance with legislation and information management policies and managing data related risks and issues.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select a single value from the options provided.
- Where a desired value is not listed contact metadata.management.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Business data steward
|
The business data steward responsible for the data.
|
|
Purpose
|
This attribute facilitates the unambiguous identification of the business data stewards and provides stewards with insight into the data for which they are accountable on behalf of their executive.
|
|
Commentary
|
The business data steward is responsible for the day-to-day management and use of the data from a business perspective. Business Data Stewards ensure all items are appropriately registered, approve access to an item and related information assets, and act as a point of contact for information about items they manage. They hold the relevant authority to make decisions about an item, its data and management. The function is commonly fulfilled by an executive level employee but can also be an APS level employee with appropriate knowledge and decision-making authority.
|
|
Controlled values
|
- Select the free text field and record a value utilising one of the following formatting options:
- Business data steward: [section / team name] Section
- Project data steward: [project name] Project
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Technical data steward
|
The technical data steward, or data administrator, responsible for the creation and/or management of the data.
|
|
Purpose
|
This attribute facilitates the unambiguous identification of the technical data stewards responsible for the creation and management of data from a technical perspective.
|
|
Additional comments
|
Technical data stewards / data administrators may support business data stewards to create and manage an item, including the creation, definition and purpose of data, improving the quality of data and implementing access arrangements for authorised users. They may:
- Create and maintain data structures for reporting and analytics.
- Manage user access control methods based on advice from data stewards.
- Advise data stewards on technical issues related to an item.
- Install, upgrade and maintain data and analytics information systems.
- Maintain, create backups and restore data and information.
A branch and section name are preferred to an individual’s contact because it is enduring and minimises the need to regularly update metadata records. Specific, individual stewardship details (including names) are recorded in the Data Stewards Register.
|
|
Obligation
|
Data Asset:
|
Optional
|
|
Data Exchange:
|
Optional
|
|
Data Transfer:
|
Not included
|
|
Controlled values
|
The technical data steward is recorded using the branch and section name, formatted as:
- [Branch Name] – [Section Name]
|
|
Example(s)
|
- Business Intelligence and Performance Branch – Digital and Telephony Section
|
|
|
Technical contact point
|
The section or team email address or contact web form used to request technical access to, or technical information about, the data.
|
|
Purpose
|
This attribute identifies technical subject matter experts who may be different to the business data steward and may be contacted for technical advice such as how an item is generated.
|
|
Commentary
|
The contact point is recorded as the team or section that can provide additional information related to an item. The Technical data steward’s team or section shared mailbox address is preferred because it is generic and enduring, minimising the need to regularly update metadata records.
|
|
Controlled values
|
- At least one valid email address or contact web form.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Keywords
|
Standardised terms that describe the subject matter of the data.
|
|
Purpose
|
This attribute is used to describe topics covered by the data, using language consistent across the agency and broader government data inventories. When selecting keywords, consider what search terms a user may choose when searching for the item, providing as much granularity as practicable.
- It answers the question: What is in this data?
|
|
Commentary
|
The field is used in conjunction with the Definition and Purpose details fields for identifying and describing an item. There are two unique types of keywords which can be assigned:
|
|
Controlled values
|
- Select the free text field and record one or more value utilising, following the below guidelines:
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
- Business support and regulation, Workforce, Indigenous affairs
|
- Community services, Department of Social Services (DSS)
|
|
|
|
Population
|
The demographic coverage details of the data.
|
|
Purpose
|
This attribute provides details describing who the data is about.
- It answers the question: Who is the data about?
|
|
Controlled values
|
- At least one complete sentence.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
- All people over the age of 45 who receive Job Seeker payment.
|
|
|
Sensitive data
|
The type of sensitivity of the data asset, where applicable.
|
|
Purpose
|
This attribute alerts users to protections and procedures required during access, storage, transport, and disposal of the data.
- It answers the question: What is in this data?
|
|
Commentary
|
The Privacy and Secrecy hub provides sensitive data information, definitions and resources.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided:
- N/A (not sensitive): no sensitive data is contained within an item.
- Personal privacy: restrictions on access to, or use of, personal information collected for which can be used to identify an individual.
- Legal privilege (including commercial-in-confidence): restrictions on access to, or use of, information covered by legal privilege.
- Legislative secrecy: restrictions on access to, or use of, information covered by secrecy provisions.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Personal or sensitive information details
|
The type/s of personal or sensitive information contained in the data.
|
|
Purpose
|
This attribute provides further granularity and details regarding any personal or sensitive information contained in the data to enable identification and retrieval of assets which contain different types of personal or sensitive information. |
|
Commentary
|
The Office of the Australian Information Commissioner (OAIC) - What is Personal / Sensitive Information resource provides examples and resources to identify and distinguish information.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided:
- Personal data: Name, Date of birth, Address, Phone and contact details, Bank details, Employment details, Gender, Internet Protocol (IP) address, Personal identifiers, Personal identifiers (Customer), Personal identifiers (Staff), Proof of identity documents, Relationship details, Services applied for or received, Voice recordings.
- Sensitive data: Biometric information, Biometric templates, Criminal record, Genetic information, Health information, Indigenous status, Racial or ethnic origin, Membership of a political association, Membership of a professional or trade association, Membership of a trade union, Philosophical beliefs, Political opinions, Religious beliefs or affiliations, Sexual orientation or practices.
- Where a desired value is not listed contact metadata.management
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
- Conditional - mandatory if item classification is OFFICIAL: Sensitive
|
|
- Conditional - mandatory if item classification is OFFICIAL: Sensitive
|
|
|
|
- Services applied for or received
|
|
|
Data granularity
|
The lowest level of detail or data granularity which is available in the data.
|
|
Purpose
|
This attribute enables users to find, categorise and evaluate the fitness of the data to their needs, and understand implications for the appropriate management of that data.
|
|
Commentary
|
Where data contains multiple levels of granularity, select multiple values accordingly.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided:
- Person unit record sensitive identifiable: personal and sensitive information which can or does identify an individual.
- Person unit record identifiable: personal information which can or does identify an individual.
- Person unit record de-identified: personal information which has undergone a cleansing process to remove personal identifiers.
- Unit record non-personal information: data that is not personally identifiable but can still be linked to an individual through auxiliary information.
- Aggregate: combined data used to express broad view of a population or dataset via summary information(s) or performance measures.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
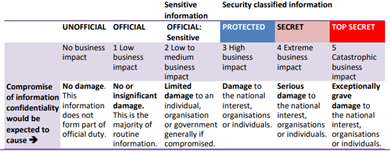
Security classification
|
<p>The <a href="https://www.protectivesecurity.gov.au/">Protective Security Policy Framework (PSPF)</a> classification applied to the data.</p>
|
|
Purpose
|
This attribute ensures data is handled, communicated, disclosed and stored appropriately and relates to the Sensitive Data and Rights attributes. |
|
Commentary
|
Specify the classification appropriate for the data, taking into consideration whether the data contains personal or sensitive information. If data contains multiple components, record the highest security classification.
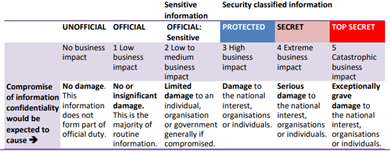
For further information, refer to the agency’s Security Markings intranet page.
|
|
Controlled values
|
- Select the drop-down box and record a value from one of the following options:
- UNOFFICIAL, OFFICIAL, OFFICIAL: Sensitive, PROTECTED, SECRET, TOP SECRET.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Resource type
|
The type of data being described, in terms of its format.
|
|
Purpose
|
This attribute assists users to understand how the data is formatted.
|
|
Commentary
|
A full list of resource type definitions and examples can be found at Dublin Core - Resource Types.
|
|
Controlled values
|
- Select the drop-down box and select a single value from the options provided:
- Collection: an aggregation of items where the resource(s) is described as a group; its parts may be separately described and navigated.
- Dataset: structured information encoded in lists, tables, databases, etc.
- Event: a non-persistent, time-based occurrence. o Image: the content is primarily symbolic visual representation other than text.
- Interactive resource: resources which require interaction from the user to be understood, executed, or experienced.
- Model: an abstraction of a real thing.
- Party: a person, organisation, cultural group or institution.
- Physical Object: a non-human object or substance.
- Place: a geographic area.
- Service: a system that provides one or more functions of value to the end user.
- Software: a computer program in source or compiled form which may be available for installation non-transiently on another machine.
- Sound: a resource whose content is primarily audio or intended to be realised in audio.
- Text: a resource whose content is primarily words for reading.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Format
|
The distribution format of the data.
|
|
Purpose
|
This attribute provides certainty with data identification and assists suitability for use assessments.
|
|
Commentary
|
Supplements Resource type to provide additional granularity to how the data is formatted and must align with the catalog formatting options in which the data is contained (where applicable).
|
|
Controlled values
|
- For structured data: provide the name and/or type of database. Common examples include:
- Apache Hive, Azure SQL, IBM DB2, M204, Microsoft SQL Server, MongoDB, Oracle Database, PostgreSQL, SAP HANA, Teradata.
- For products and programs: provide the relevant file extension. Common examples include:
- PDF, DOCX, CSV, JSON, XLS, XLSX, DAT, XML, SQL, SAS, JPEG, JPG, PNG, BMP, GID, ZIP, TXT, HTML etc.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
File size
|
The measure of the digital storage needed by the data.
|
|
Purpose
|
This attribute provides data administrators with information to assist with managing potential storage issues and assists users with the logistics of requesting and storing data.
|
|
Commentary
|
Where file size is constantly changing, provide an indicative size or an indicative size range for your item. This information may be sourced through the agency’s IT or data management department.
|
|
Controlled values
|
- For databases: provide the number of tables stored in the catalog, for example:
- For digital assets: provide a number and units, for example:
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Access instructions
|
The instructions for users to obtain access to the data.
|
|
Purpose
|
This attribute provides user guidance for how to gain access to the data. |
|
Commentary
|
The access instructions may include details such as the restrictions or conditions placed on access to the data, any security resource or role required, e.g. via the ICT Security Portal (ISP) or the directory file path representing the location of the data.
|
|
Controlled values
|
- At least one complete sentence.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
- Access is restricted to Services Australia employees who hold a baseline security clearance and can establish a ‘need to know’ justification. Request the RU_DEV_EDW_DATABASE_LEGO role via the ICT Security Portal (ISP) for access.
|
|
|
Data audience
|
The intended audience, or consumers, of the data.
|
|
Purpose
|
This attribute identifies the intended audience of the data, as well as secondary consumers or recipients.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided:
- Group: a group within the agency, led by a deputy CEO, responsible for a generalised area of focus, reporting to the CEO and made up via a collection of divisions and branches.
- Division: a division within the agency, led by an SES GM, responsible for a collection of focus areas, reporting directly to a deputy CEO and made up via a collection of branches.
- Select the free text field to record the audience branch, business area or program (if required).
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
Distribution method
|
The method(s) used to distribute or provide access to the data.
|
|
Purpose
|
This attribute supports the identification and management for distribution and access methods used across the agency.
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the following options:
- Automated: reports are self-triggered and self-sending, requiring no intervention.
- Self Service: reports are open to users who can select and view the current report.
- Static Report: reports will not update or change without another produced version.
- External: reports are sent outside of Services Australia.
- Branch Only: report visibility is limited to the branch responsible for its creation.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Sharing authority
|
The legal mandates or data sharing arrangements under which the data can be supplied.
|
|
Purpose
|
This attribute identifies the document or documents providing authority for data to be shared or published and the documents which detail arrangements under which data is exchanged. |
|
Commentary
|
The sharing authority should reference documents such as specific acts/sections of legislation; Public Interest Certificate (PIC); Public Data Sharing Protocols; Bilateral agreements or Contracts
|
|
Controlled values
|
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Records authority
|
<p>The record authority which the data is subject, under the relevant <a href="https://www.naa.gov.au/information-management/records-authorities">National Archives of Australia (NAA)</a> records authority.</p>
|
|
Purpose
|
This attribute ensures disposal actions are clear and apparent, streamlining compliance with the relevant legal instrument governing keeping, transferring, or disposing of the data to enable compliance with the Privacy Code and record keeping requirements
|
|
Commentary
|
Resources below provide further information on record authorities and their usage by the agency:
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided:
- Where a desired value is not listed contact metadata.management.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
- 2011/00714998 - Medicare Australia
|
|
|
|
|
Records class no. and disposal
|
<p>The record class number and disposal action to which the data is subject under the relevant <a href="https://www.naa.gov.au/information-management/records-authorities">National Archives of Australia (NAA) </a>records authority.</p>
|
|
Purpose
|
This attribute ensures disposal actions are clear and apparent, supporting compliance with disposal requirements and ensures alignment with the proposed Records Authority.
|
|
Commentary
|
Resources below provide further information on record authorities and their usage by the agency:
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
- Class Number 20158 - Destroy 10 years after last action
|
|
|
|
|
Data asset class
|
The type of data according to its stage in the data lifecycle.
|
|
Purpose
|
This attribute differentiates data set which comprise the agency’s data inventory according to the level of development, curation and reusability of the data.
|
|
Commentary
|
The classification makes clear the breadth of use cases for an item using language consistent across government data inventories and supports contributions to the Australian Government Data Catalogue (AGDC).
|
|
Controlled values
|
- Select the drop-down box and select a single value from the options provided:
- Source system data: collected and managed in a transactional or operational system as the system of record or authoritative data source.
- Prepared data: prepared, loaded or made ready for further use or analysis but has not yet been significantly transformed or curated for a specific purpose.
- Curated data: undergone an intensive process to authenticate, provision and ensure its quality, then it has been cleansed, organised and validated making it readily available, usable and accurate for end users to explore, analyse and report.
- Data product: result of data curation which has prepared it for specific users or use cases.
- Further values exist for records not a part of the data inventory, but should still be categorised:
- Data exchange: identifies a record as a data exchange, as registered in CITADEL. A Data Exchange will be the parent record for one or more Data Exchange Transfers.
- Data exchange transfer: identifies a record as a data exchange transfer, as registered in CITADEL. It must be connected to a parent Data Exchange record. The Data Exchange Transfer contains specific data elements and is shared with an exchange partner.
- Administrative record: identifies a record as a ‘container’ for which data cannot be described meaningfully as an asset itself, but may contain logical groupings of data that can or contains non-persistent data
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
AGDC status
|
<p>An indicator of the status of a record for contribution to the <a href="http://www.dataplace.gov.au/search/">Australian Government Data Catalogue</a> (AGDC).</p>
|
|
Purpose
|
This attribute assists with the identification of suitable records for contributing to the AGDC, including whether a record has already been contributed and should be maintained. |
|
Commentary
|
The AGDC Record Contributions guidelines identify the types of item records suitable to the AGDC and clarifies the roles and responsibilities, processes and technologies that enable this to occur.
|
|
Controlled values
|
- Select the drop-down box and select a single value from the options provided:
- Unsuitable (non-custodian): an external agency is responsible for an item and has the authority for sharing and disclosure. See Data Custodian attribute.
- Unsuitable (sensitivity): an item relates to sensitive business functions and, by making this information available, poses an unacceptable risk to the agency.
- Unsuitable (class/format): it is not the appropriate data asset class and/or it is a product to which the agency cannot provide access.
- Suitable: an item has been assessed as meeting the inclusion criteria for contribution to the Catalogue.
- Published: an item record has been published to the Catalogue.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
- Unsuitable (non-custodian)
|
|
|
|
|
Data custodian
|
<p>The agency that is responsible for the data asset and has the authority for sharing and disclosure. The data custodian can differ from the publisher (see Publisher attribute). An agency may also be a data custodian under the <a href="https://www.legislation.gov.au/Details/C2022A00011">Data Availability and Transparency Act 2022</a> if:</p>
<ol>
<li>“[they are] a Commonwealth body; and</li>
<li>[are] not an excluded entity; and</li>
<li>either:;
<ul>
<li>controls public sector data (whether alone or jointly with another entity), including by having the right to deal with that data; or</li>
<li>has become the data custodian of output of a project in accordance with section 20F.”</li>
</ul>
</li>
</ol>
|
|
Purpose
|
This attribute identifies the responsible party of an item who has authority for sharing or disclosure. |
|
Commentary
|
Services Australia collects and manages a vast amount of customer data to administer payments and services for programs on behalf of itself and policy departments, defined as:
- Policy departments are considered custodians of data collected for the administration on services and remain responsible for its sharing and disclosure.
- Services Australia is considered custodian of data collected for operational performance, agency workforce or corporate activities and remain responsible for its sharing and disclosure.
Bilateral agreements may stipulate different or specific data custodian arrangements.
|
|
Controlled values
|
- Select the drop-down box and select a value from one of the following options:
- Services Australia, Department of Social Services, Department of Health and Aged Care, Department of Education, Department of Employment and Workplace Relations, Department of Home Affairs, Department of Veterans' Affairs
- Where a desired value is not listed and the entity appears on one of the following resources, contact metadata.management:
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Publisher
|
The agency who has published the data, making it formally available for use.
|
|
Purpose
|
This attribute differentiates items originating within the agency from those sourced externally, e.g. through data exchange arrangements with other government agencies or departments. |
|
Commentary
|
The publisher is the agency that formally produces and is responsible for the release of the data and controls any future version release. The publisher may or may not be the Data Custodian (see Data Custodian attribute).
|
|
Controlled values
|
- Select the drop-down box and select a value from one of the following options:
- Services Australia, Department of Social Services, Department of Health and Aged Care, Department of Education, Department of Employment and Workplace Relations, Department of Home Affairs, Department of Veterans' Affairs
- Where a desired value is not listed and the entity appears on one of the following resources, contact metadata.management:
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Certification date
|
The most recent date a data steward reviewed and certified the record.
|
|
Purpose
|
This attribute enables users to keep record of when a certification review was completed.
|
|
Commentary
|
The value and criticality rating determines the frequency of certification reviews via the cadence:
- Critical, very high and high values: data must be certified every 12 months.
- Medium value: data must be certified every 24 months.
- Low value: data be reviewed when there are changes to the asset or steward details.
|
|
Controlled values
|
- A date entered using the date picker or manually entered in year first format (yyyy-mm-dd).
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Critical business function(s)
|
The indication of whether the data enables an identified critical business function.
|
|
Purpose
|
This attribute contributes to the Data Asset Value and Criticality Assessment profile, which is established to support business areas in applying proportionate data governance to data they hold.
- It answers the question: Is the data used to enable any of the critical business functions listed?
|
|
Commentary
|
All value and criticality fields must be considered under the guidance of the:
|
|
Controlled values
|
- Select the Plus (+) button to browse and select one or more values from the options provided.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
- Crisis Payment, Social Work
|
|
|
|
|
Critical system indicator
|
The indication of whether the data enables an identified critical system.
|
|
Purpose
|
This attribute contributes to the Data Asset Value and Criticality Assessment profile, which is established to support business areas in applying proportionate data governance to data they hold.
- It answers the question: Does the data enable an identified critical system?
|
|
Commentary
|
All value and criticality fields must be considered under the guidance of the:
|
|
Controlled values
|
- Critical systems are identified in the Services Australia Architecture Library SLA Level, where your system is identified as critical:
- Select the Plus (+) button to browse and select one or more values from the options provided.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Data asset value
|
The information that describes the value of the data to the agency.
|
|
Purpose
|
This attribute contributes to the Data Asset Value and Criticality Assessment profile and supports the identification of the most appropriate criticality rating where a default value isn’t assignable, based on the valuation of assessment responses and the consequences or impact for the agency.
|
|
Commentary
|
All value and criticality fields must be considered under the guidance of the:
|
|
Controlled values
|
- Select the Plus (+) button to browse and select a single value for each question from the options provided.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
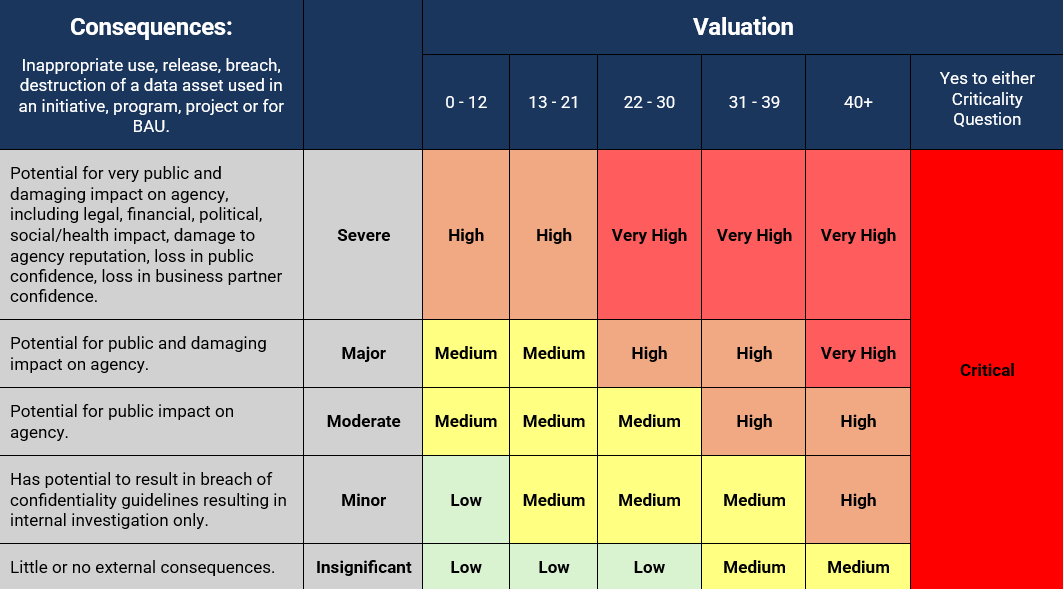
Value and criticality
|
The rating applied to the data, determined by the value and criticality matrix.
|
|
Purpose
|
This attribute is the result of the Data Asset Value and Criticality Assessment profile and establishes an item’s review cadence, works to ensures data is protected, used effectively, and supports critical business operations.
|
|
Commentary
|
Use the results of the criticality and value assessments to determine the final value rating according to the matrix below:
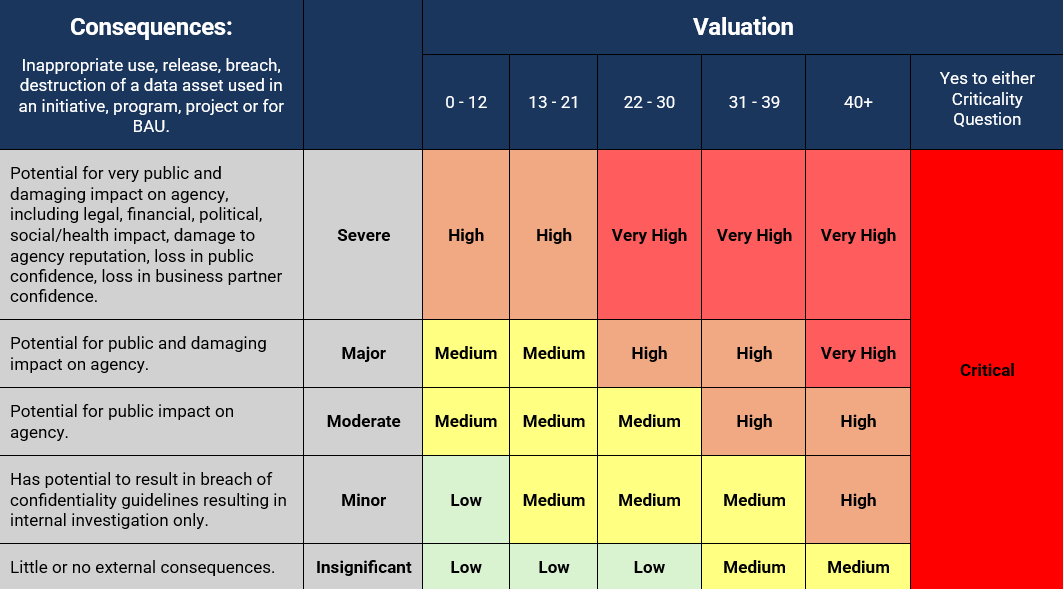
Use the sum of the answers to the value questions to determine placement on the valuation axis and consider the consequences if the asset were to be lost, unavailable or compromised to find placement on the consequences axis.
All value and criticality fields must be considered under the guidance of the:
|
|
Controlled values
|
- Select the Plus (+) button to browse and select a single value from the options provided:
- Low: The data asset may not be expected to provide meaningful future benefit to the agency but may be useful for future discoverability.
- Medium: The data asset is not deemed critical but may contain personal information, or support other business functions, may be subject to scrutiny, or be limited in volume.
- High: The data asset may be expected to provide significant benefit to the agency and may contain personal information, or support other business functions, and may be subject to scrutiny.
- Very High: The data asset supports vital business functions or systems or poses a risk to privacy and trust.
- Critical: The data asset is used to enable or support the effective operation of identified critical systems or critical business processes.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Exchange delivery method
|
The transmission method for data exchange transfer.
|
|
Purpose
|
This attribute identifies the specific transfer method used to provide or receive data.
|
|
Commentary
|
- The delivery methods are represented as either online or offline as defined below:
- Online Delivery Method: a digital method of communication or transfer.
- Offline Delivery Method: a physical method of communication or transfer.
|
|
Controlled values
|
- Select and record a single value from the options provided:
- Online Delivery Methods: Application Programming Interface (API), ArcGIS Feature Server, ATO Data Transfer Protocol, Bluezone-File Transfer Protocol (FTP), Business Online Services, Business Portal, Cuba, Digital Gateway, ECXpert, External Data Exchange (EDX), Government to Government Server (GSO), HP Autonomy Process Automation, NZ Liaison Platform, IBM Sterling, Informatica, Line Printer Daemon, Managed File Transfer Facility, MQ Messaging, Open ID Connect, Optus Evolve, Organisation Online Mail, PGP, Protected Enclaves PAD, Public Key Infrastructure, Secure File Transfer Protocol (SFTP), Secure Network Interface Link, SIGBOX, Sterling Mail Transfer, Web Service Call, Xcomm, YSPBDOHA.
- Offline Delivery Methods: CD/DVD, Drop Box, Email, Encrypted USB, External Hard Drive, Facsimile, Hand Delivery, Non-Registered Post, Phone Call, Post, Registered Post.
|
|
Obligations and examples
|
| Data asset |
Data exchange |
Data transfer |
|
|
|
|
|
|
|
|
|
|
Exchange transfer direction
|
An indication of whether a data exchange transfer is inbound or outbound in relation to the agency recording the exchange.
|
|
Purpose
|
This attribute assists users identify whether a data transfer is providing data to a partner entity (outbound) or receiving data from a partner entity (inbound). |
|
Commentary
|
An exchange is comprised of one or more transfers, which can be either inbound or outbound in relation to the agency creating the record. If data is mutually exchanged, (both sent and received) this is recorded as two separate transfers.
|
|
Controlled values
|
- Select and record a single value from the options provided:
- Inbound: Services Australia is receiving data from a partner entity.
- Outbound: Services Australia is providing data to a partner entity.
|
|
Obligations and examples
|
|
Data asset
|
Data exchange
|
Data transfer
|
|
|
|
|
|
|
|
|
|
|
Physical Name (unused)
|
|
|
|
Services Australia Keywords (unused)
|
Word(s) or terms that describe the data asset subject matter.
|
Note: this field is unused as of 26/08/2024.
Purpose: Provides additional high-level information regarding asset content in a manner that facilitates discovery, linkage and descriptive analysis of data asset records.
Obligation: Optional
Additional comments: Keywords should be meaningful and relevant to the data asset. Select one or more keywords from the provided list. For a list of available keywords and definitions, refer to the the Data Asset Registration User Guide.
Controlled values: Select one or more keywords from the provided list - select the Plus (+) button to browse and add keywords. Where a desired keyword is not listed, contact metadata.management.
Example(s):
- Aged care services
- Application / claim
ONDC alignment: N/A |
|
Sensitive Data Type (unused)
|
The type of sensitivity of the data asset, where applicable.
|
Note: this field is unused as of 26/08/2024.
Purpose: To provide further detail about the type of sensitivity associated with the data.
Obligation: Conditional (mandatory if Security Classification is “OFFICIAL: Sensitive”)
Additional comments: If Security Classification has value “OFFICIAL: Sensitive”, provide the type of sensitivity. Provide one or more values from the list of options. For a definition of sensitive information refer to the Privacy and Secrecy intranet page. Record one or more values from the options provided - select the Plus (+) button to browse and add values
Controlled values: N/A (not sensitive), Personal privacy, Legal privilege (including commercial-in-confidence), Legislative secrecy
Example(s):
ONDC alignment: Sensitive Data (additional attribute) |